THE ANTI‐FRAUD ENVIRONMENT: THE BLUEPRINTS, THE FOUNDATION, THE GROUND FLOOR The Architect’s Blueprint: Establishing the Framework
THE ELEMENTS OF ANTI‐FRAUD PROGRAM DESIGN
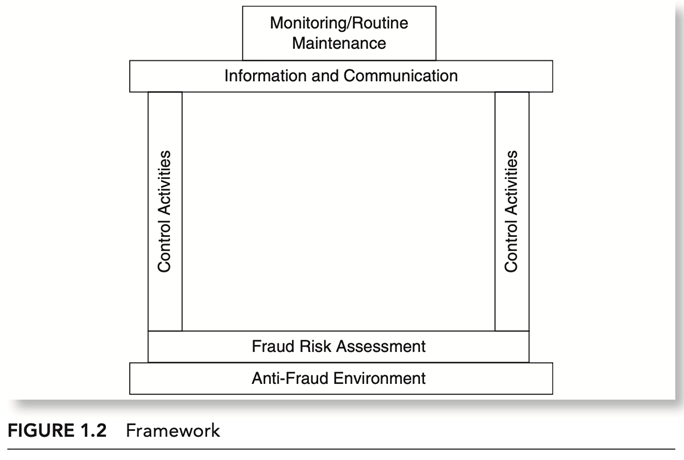
The original COSO framework outlines five elements of internal control design: (1) the control environment, (2) risk assessment, (3) control activities, (4) information and communication, and (5) monitoring. While keeping with the intent of this structure, I have modified the names and format of some of these elements to best present the architect’s blueprint for the design process of the anti‐fraud program. Each reference to program design in this book includes a categorization of the guidance into one or more of these elements. As the elements are addressed, more specific definitions of each will be provided. However, a basic description of each element is provided next to familiarize you with the concepts.
ANTI‐FRAUD ENVIRONMENT
The anti‐fraud environment is best described as the tone at the top. What is the level of concern for fraud prevention from the business owner, the board of directors, or those bodies tasked with governance of the company? If there is no concern from these parties, assuredly there will be no concern from those below. Conversely, if the owners or governing bodies of a company exhibit an appropriate concern for fraud prevention, then the staff should follow suit. Evidence of these concerns is demonstrated through the anti‐fraud envi- ronment: the environment that includes processes and policies established to address fraud risk.
FRAUD RISK ASSESSMENT
However, the responsibility for an effective anti‐fraud program lies with those with governing authority over the company. Those individuals may certainly seek the advice of the accountant types in designing the anti‐fraud program, but the overall responsibility cannot be delegated away from the governing body.
CONTROL ACTIVITIES
This element of internal control is represented by the actual checks and bal- ances that exist. Control activities are specific. One of the most common is the bank reconciliation. The performance of the bank reconciliation is a major business process that can also function as an outstanding control activity. If done correctly, bank reconciliations serve not only to prevent fraud but also to detect fraud. Requiring dual signatures on checks over a certain dollar amount and physical inventory counts are excellent examples of specific control activi- ties. Their design is of such importance that I have devoted several chapters to control activities as they apply to various financial areas common in most businesses.
INFORMATION: PROGRAM DOCUMENTATION
In our journey to design the best possible anti‐fraud program for your busi- ness, we have established a proper anti‐fraud environment, assessed the areas of greatest fraud risk, and designed specific control activities to address those risks. Now we need to document that system.
The information aspect of this element speaks to the need to commit this program to written form. I consider myself moderately intelligent, but there is no way I would be able to memorize all of the aspects of an anti‐fraud program. Committing all of this to written form sounds relatively simple, yet I constantly encounter companies whose anti‐fraud strategies are known only by those performing the activities. What happens when these individuals are hit by the proverbial bus? Once they’re gone, so is the program, because the replacements won’t know it exists. While simple in concept, the process of documentation can become too complex very quickly. This book includes a separate chapter devoted to how to avoid the pitfall of overcomplexity. Remember our motto: Simple practicality.
COMMUNICATION: THE COMPANY FRAUD TRAINING PROGRAM
Once the program is in written form, it must be communicated to staff, to those who will be responsible for carrying out the program. Do we send out memos? Do we give everyone a binder? Do we have live meetings? Is the program posted on our intranet? Do we periodically conduct training for staff as to how the program works? Do we seek input on problems encountered in carrying out the designed controls? Yes. The answer is a resounding yes. All of these com- bined represent the best communication efforts. Communication is important in both our personal and business relationships. My wife and I have been married for 30 years. Without proper communication, I’m not sure we could have made it this long. Suppose we left our wedding ceremony 30 years ago and never spoke again. That’s ludicrous; that’s silly to even think about. Yet, more companies than not treat the communication of the anti‐fraud program exactly like this. The work is done. Someone said we had to do it. So we did it. We put it in the most beautiful binder imaginable! Then we proudly put it on the shelf and never looked at it again. That’s ludicrous; that’s silly to even think about.
MONITORING AND ROUTINE MAINTENANCE
The second most neglected element in anti‐fraud program design is monitor- ing and routine maintenance. Monitoring is the built‐in process of periodically determining compliance with all aspects of the anti‐fraud program. If certain staff members are not complying with the controls in place, we should go the extra step and ask why. Is it a problem with the individual or with the design of the control? Regardless of how this question is answered, there is either some- one or something that needs to be fixed.
An anti‐fraud program is not a static program. It is a living, breathing document that needs to change based on operational changes. If we don’t ever monitor the controls for effectiveness and efficiency, how will we know what needs changing?
Consider in our building metaphor that we have completed the construc- tion of our new home. Obviously, we will move in and live there, possibly for- ever. Let’s assume that through the years we perform no routine maintenance on this home. Eventually it will fall apart and lose all of its effectiveness as a home. Allowing this to happen to your home would be considered extremely irresponsible. The monitoring element of the anti‐fraud program is essential to the accomplishment of routine maintenance. Without it, the program will eventually fall apart and lose its effectiveness as a program.
These six elements provide the framework into which everything we address from this point forward will fit. Think of this framework as the architect’s blue- print for a new home. It is the plan for going forward. Without this plan, this blueprint, this framework, our structure will be unsound, ineffective, and pos- sibly even dangerous.
The anti‐fraud environment is the foundation, the fraud risk assessment is the ground floor, the control activities are the walls (the structure), the information and communication elements tie it all together as the ceiling, and the monitoring and routine maintenance element tops it off under one roof.
Referensi:
- Dawson, S. 2015. Internal Control – Anti Fraud Program Design for the Small Business. Wiley.
- Goldman, P. 2010. Financial Services Anti-Fraud Risk and Control Workbook. Wiley.
- 2021. Google Image.